System Access Control: The Importance of Protecting Your Data
In today’s digital age, data security is more important than ever. Companies and individuals alike rely on technology to store and manage sensitive information, from financial records to personal details. However, with this increased reliance on technology comes an increased risk of data breaches and cyber attacks. That’s where system access control comes in.
System access control is the practice of limiting access to computer systems and networks based on user permissions. This means that only authorized users are able to access certain files or systems, while unauthorized users are blocked from doing so. Access control can take many forms, such as passwords, biometric identification, or security tokens.
The benefits of system access control are numerous. Firstly, it helps to protect sensitive information from unauthorized access. This is particularly important for businesses that handle confidential client data or financial records. By limiting who has access to this information, companies can reduce the risk of data breaches and other cyber attacks.
Access control also helps to ensure that employees only have access to the information they need to do their jobs. For example, a receptionist may not need access to the company’s financial records, while an accountant would require this information in order to perform their duties. By limiting access based on job role and responsibility, companies can reduce the risk of accidental or intentional misuse of sensitive data.
Another benefit of system access control is that it can help with regulatory compliance. Many industries have specific regulations around data security and privacy, such as HIPAA for healthcare providers or GDPR for companies operating in the European Union. By implementing strong system access controls, businesses can demonstrate compliance with these regulations and avoid costly penalties.
Implementing effective system access controls requires careful planning and ongoing maintenance. It’s important to regularly review user permissions and adjust them as necessary based on changes in job roles or responsibilities. Regularly updating passwords or other authentication methods is also critical for maintaining strong security.
In conclusion, system access control is a critical component of data security in the digital age. By limiting access to computer systems and networks based on user permissions, businesses can protect sensitive information from unauthorized access, reduce the risk of data breaches and cyber attacks, ensure regulatory compliance, and more. It’s important for businesses of all sizes to take this issue seriously and implement strong access controls to protect their data.
Essential FAQs on System Access Control: Best Practices, Security Measures, and User Activity Monitoring
- How do I set up system access control?
- What are the best practices for system access control?
- How can I secure my system from unauthorized access?
- What is the difference between authentication and authorization in access control systems?
- How can I ensure that only authorized users have access to certain resources on my network?
- What type of user roles are required for effective system access control?
- What methods can be used to enforce system access controls?
- How can I monitor and audit user activity on my network for compliance with security policies?
How do I set up system access control?
Setting up system access control requires careful planning and attention to detail. Here are some steps you can follow to implement effective access controls:
- Identify what information needs to be protected: Start by identifying the types of data that need to be protected, such as financial records, customer information, or confidential business plans.
- Determine who needs access: Once you’ve identified the data that needs to be protected, determine who needs access to it. This could include employees, contractors, or third-party vendors.
- Define user roles and permissions: Based on the users who require access, define user roles and permissions. For example, an accountant may require access to financial records while a receptionist may only need access to appointment schedules.
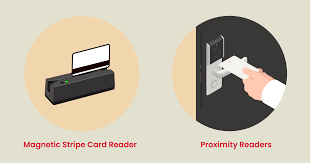
- Implement authentication methods: Choose authentication methods based on your security needs and budget. This could include passwords, biometric identification (such as fingerprint or facial recognition), or security tokens.
- Regularly review and update permissions: Regularly review user permissions and adjust them as necessary based on changes in job roles or responsibilities.
- Train employees on proper use of access controls: It’s important to train employees on the proper use of access controls and why they are important for data security.
- Monitor system activity: Implement monitoring tools that allow you to track system activity and detect any unauthorized access attempts.
By following these steps, you can establish strong system access controls that protect sensitive data from unauthorized access while ensuring that authorized users have the necessary permissions to perform their jobs effectively.
What are the best practices for system access control?
There are several best practices for system access control that organizations can follow to ensure the security of their data and systems. Here are some key practices to consider:
- Role-Based Access Control (RBAC): Implementing RBAC is a best practice for controlling system access. This means granting access based on an individual’s job function, rather than giving everyone the same level of access.
- Least Privilege: The principle of least privilege means granting users only the minimum level of access they need to perform their job functions. By limiting access, you can reduce the risk of accidental or intentional misuse of sensitive data.
- Strong Authentication: It’s important to use strong authentication methods, such as two-factor authentication or biometric identification, to verify user identities and prevent unauthorized access.
- Regular Reviews: It’s important to regularly review user permissions and adjust them as necessary based on changes in job roles or responsibilities.
- Monitoring and Logging: Monitoring and logging all system activity can help detect suspicious activity and provide evidence in case of a security breach.
- Encryption: Encrypting sensitive data both in transit and at rest can help protect it from unauthorized access.
- Password Policies: Implementing strong password policies, such as requiring complex passwords that are changed regularly, can help prevent unauthorized access due to weak passwords.
- Training and Awareness: Regularly training employees on cybersecurity best practices and raising awareness about the importance of system access control can help reduce the risk of human error leading to a security breach.
By following these best practices for system access control, organizations can better protect their data and systems from unauthorized access and reduce the risk of data breaches or cyber attacks.
How can I secure my system from unauthorized access?
There are several steps you can take to secure your system from unauthorized access:
- Use strong passwords: Ensure that all user accounts have strong passwords that are difficult to guess. Passwords should be at least 12 characters long and include a mix of uppercase and lowercase letters, numbers, and symbols.
- Implement two-factor authentication: Two-factor authentication adds an extra layer of security by requiring users to provide a second form of identification, such as a code sent to their mobile phone or a fingerprint scan.
- Limit user access: Only grant access to the system or specific files and folders to users who need it for their job role. Regularly review user permissions and revoke access when necessary.
- Regularly update software: Keep your operating system, antivirus software, and other programs up-to-date with the latest security patches to protect against known vulnerabilities.
- Use firewalls: Firewalls act as a barrier between your computer and the internet, blocking unauthorized access attempts.
- Encrypt sensitive data: Encryption scrambles data so that it can only be read by someone with the appropriate decryption key. This is particularly important for sensitive information such as financial records or personal details.
- Monitor system activity: Regularly monitor your system for suspicious activity, such as failed login attempts or unauthorized file access.
- Educate users: Train all users on best practices for data security, including how to create strong passwords, how to identify phishing emails, and how to report suspicious activity.
By following these steps, you can significantly reduce the risk of unauthorized access to your system and protect sensitive information from potential data breaches or cyber attacks.
What is the difference between authentication and authorization in access control systems?
Authentication and authorization are two different concepts in access control systems, although they are often used together to provide secure access to resources.
Authentication is the process of verifying the identity of a user or system. This can be done through various means, such as passwords, biometric identification, or security tokens. The goal of authentication is to ensure that the person or system trying to access a resource is who they claim to be.
Authorization, on the other hand, is the process of granting or denying access to a resource based on a user’s identity and permissions. Once a user has been authenticated, they must then be authorized to access specific resources. This can be done through role-based access control (RBAC), where users are assigned specific roles that determine what resources they can access; attribute-based access control (ABAC), where users are granted access based on specific attributes such as job title or security clearance; or other methods.
In simpler terms, authentication confirms who you are while authorization determines what you are allowed to do. For example, when you enter your username and password into a website login form (authentication), the website then checks your account permissions to determine whether you have permission to view certain pages or perform certain actions (authorization).
Both authentication and authorization are important components of an effective access control system. By verifying identities and limiting resource access based on permissions, businesses can ensure that their data remains secure and confidential.
How can I ensure that only authorized users have access to certain resources on my network?
There are several steps you can take to ensure that only authorized users have access to certain resources on your network:
- Implement strong authentication methods: This can include passwords, security tokens, biometric identification, or a combination of these methods. Ensure that passwords are complex and changed regularly.
- Use role-based access control (RBAC): This allows you to assign specific permissions to users based on their job roles and responsibilities. For example, an HR manager may have access to employee records while a receptionist may not.
- Regularly review user permissions: It’s important to regularly review user permissions and adjust them as necessary based on changes in job roles or responsibilities.
- Limit physical access: Ensure that physical access to servers and other network resources is restricted to authorized personnel only.
- Monitor network activity: Use tools such as intrusion detection systems (IDS) or security information and event management (SIEM) systems to monitor network activity and detect any unauthorized access attempts.
- Train employees on security best practices: Educate employees on the importance of data security and provide training on how to identify and report potential security threats.
By implementing these measures, you can help ensure that only authorized users have access to certain resources on your network, reducing the risk of data breaches and other cyber attacks.
What type of user roles are required for effective system access control?
Effective system access control requires different types of user roles to be defined and implemented. Here are some common user roles that are necessary for effective system access control:
- System administrators: These are the users responsible for managing the computer systems and networks. They have the highest level of access to the systems and are responsible for setting up user accounts, defining user permissions, and monitoring system usage.
- Power users: These are users who require more access than standard users but less than system administrators. They may have elevated privileges to perform certain tasks or access specific data.
- Standard users: These are regular employees or individuals who require access to specific systems or data to perform their job duties. Their access is limited based on their job role and responsibilities.
- Temporary users: These are users who require temporary access to a system or network, such as contractors or vendors. Their access is limited in both time and scope.
- Auditors: These are users who monitor and review system activity to ensure compliance with regulations and policies. They have limited access to the systems but can view logs and other data related to system usage.
By defining these user roles, businesses can implement effective system access controls that limit unauthorized access, ensure compliance with regulations, and protect sensitive information from cyber threats. It’s important for businesses to regularly review these roles and adjust them as necessary based on changes in job roles or responsibilities, as well as changes in technology or regulatory requirements.
What methods can be used to enforce system access controls?
There are several methods that can be used to enforce system access controls. Here are some examples:
- Passwords: Passwords are the most common method of enforcing system access controls. Users are required to enter a unique username and password combination to gain access to a system or network.
- Biometric identification: Biometric identification involves using a person’s unique physical characteristics, such as fingerprints or facial recognition, to verify their identity and grant access.
- Security tokens: Security tokens are small devices that generate a unique code that is required for access. These codes change frequently, making it more difficult for unauthorized users to gain access.
- Role-based access control (RBAC): RBAC is a method of granting access based on job roles and responsibilities. Users are only given access to the information and systems they need to perform their job duties.
- Mandatory Access Control (MAC): MAC is a security model that restricts user access based on predefined security policies set by the system administrator.
- Discretionary Access Control (DAC): DAC is another security model that allows users to determine who has access to their data and what level of access they have.
- Two-factor authentication (2FA): 2FA involves using two methods of authentication, such as a password and security token, to grant access.
- Single sign-on (SSO): SSO allows users to log in once and gain access to multiple systems or applications without having to enter their credentials again.
Overall, the method used for enforcing system access controls will depend on the specific needs of an organization and the level of security required for their data and systems. It’s important for businesses to regularly review their security measures and adjust them as necessary based on changes in technology or threats from cyber attacks.
How can I monitor and audit user activity on my network for compliance with security policies?
Monitoring and auditing user activity on your network is an important part of maintaining security and ensuring compliance with security policies. Here are some steps you can take to effectively monitor and audit user activity:
- Define your security policies: Before you can monitor and audit user activity, you need to have clear security policies in place. These policies should outline what types of activities are allowed on the network, what types of activities are prohibited, and what consequences will result from policy violations.
- Deploy monitoring tools: There are a variety of tools available for monitoring user activity on your network, including intrusion detection systems (IDS), security information and event management (SIEM) systems, and endpoint detection and response (EDR) solutions. These tools can help you track user logins, file transfers, application usage, and other activities that may pose a risk to your network.
- Set up alerts: Once you have monitoring tools in place, it’s important to set up alerts that notify you when certain events occur. For example, you may want to receive an alert when a user fails to log in multiple times or when a file is transferred outside of authorized channels.
- Conduct regular audits: In addition to real-time monitoring, it’s important to conduct regular audits of user activity on your network. These audits should review logs from all relevant systems and applications to identify any suspicious or unauthorized activity.
- Enforce consequences for policy violations: Finally, it’s important to enforce consequences for policy violations in order to deter future misconduct. Depending on the severity of the violation, consequences may include warnings, suspension or termination of access privileges, or even legal action.
By following these steps, you can effectively monitor and audit user activity on your network for compliance with security policies. This will help you identify potential threats before they become serious issues and maintain a secure environment for your organization’s data and assets.